Introduction
Security and privacy are the major concerns of the digital world today. With the increasing number of online transactions, data breaches and cyberattacks are becoming more frequent. In such a situation, developing secure communication channels has become vital. One of the ways of ensuring security is by using a hashing algorithm. SHA512 Hash is one such algorithm that is widely used to secure online communication.
Understanding SHA512 Hash
SHA512 Hash is a secure hashing algorithm that uses a 512-bit message digest. It was published by the National Security Agency (NSA) in 2001 as a part of the Secure Hash Standard (SHS). The algorithm is widely used in digital signatures, message authentication codes (MACs), and other cryptographic applications.
SHA512 Hash works by taking an input message of any length and generating a fixed-length 512-bit output called a hash value. The hash value is unique to the input message and cannot be recreated from the hash value. The algorithm has several rounds of operations that include bitwise operations, modular arithmetic, logical operations, and logical shifts.
Key Features of SHA512 Hash
The key features of SHA512 Hash are:
- It generates a 512-bit message digest, which makes it more secure than its predecessors.
- It is faster and more efficient than other similar algorithms.
- It is widely used and tested, making it a reliable hashing algorithm.
Using SHA512 Hash
SHA512 Hash can be used in various scenarios by developers. It can be used to:
- Secure online communication channels like emails, chats, and file transfers.
- Generate unique identifiers for data records, files, and other digital assets.
- Verify the integrity of files and data transmitted over a network.
- Verify digital signatures and authenticity of documents.
Sample code or commands
Here is a sample Python code that generates a SHA512 Hash:
import hashlib
message = 'Secret Message'
hash_object = hashlib.sha512(message.encode())
hex_dig = hash_object.hexdigest()
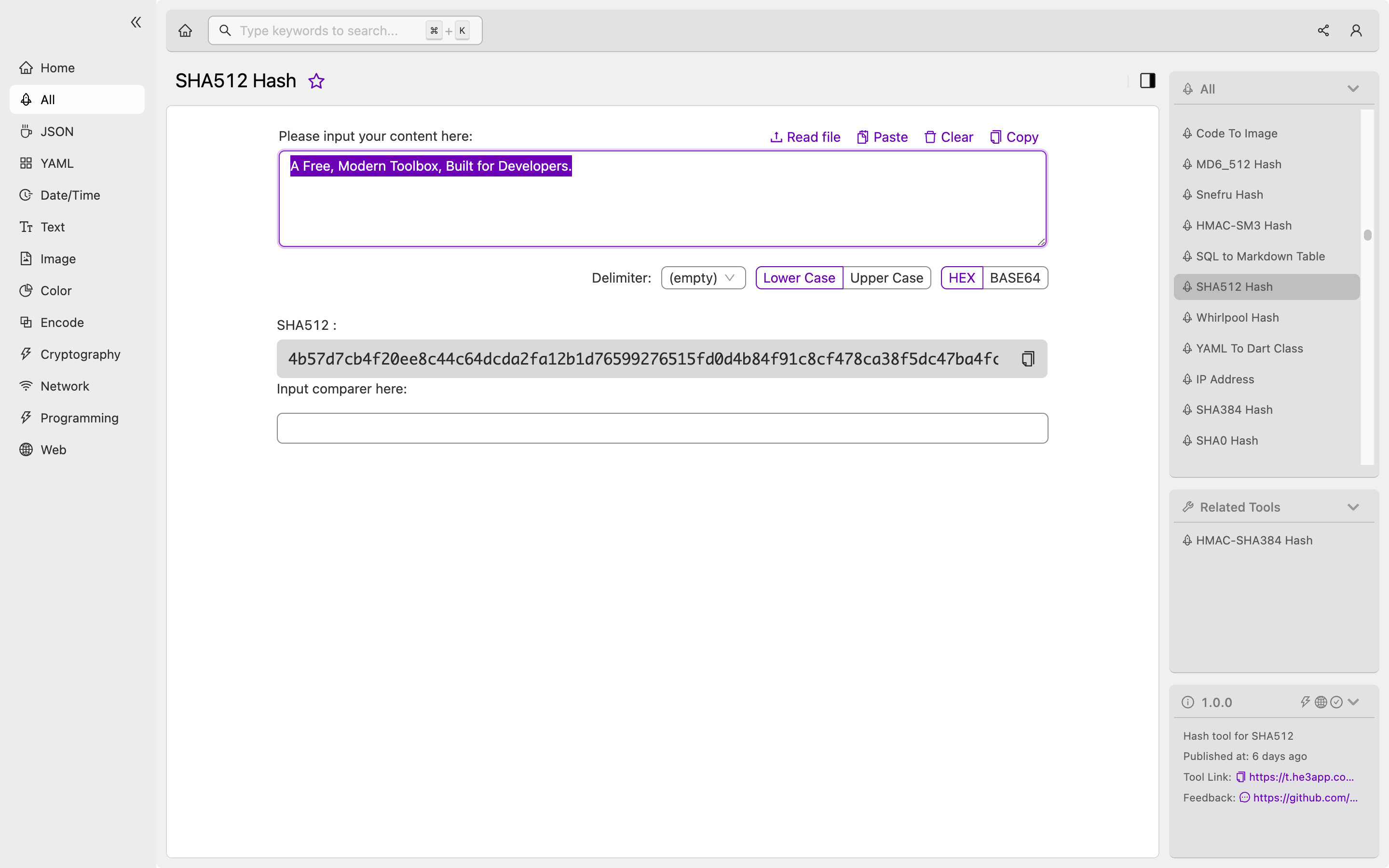
print(hex_dig)Or you can use SHA512 Hash tool in He3 Toolbox (https://t.he3app.com?qi6h ) easily.
Misconceptions and FAQs
Some misconceptions and FAQs related to SHA512 Hash are:
Is SHA512 Hash the same as encryption?
No, SHA512 Hash is not the same as encryption. Encryption is the process of converting plaintext into ciphertext, while SHA512 Hash is a one-way function that generates a fixed-length hash value.
Can SHA512 Hash be reversed?
No, SHA512 Hash is a one-way function and cannot be reversed. It is computationally infeasible to recreate the input message from the hash value.
Is SHA512 Hash vulnerable to attacks?
No, SHA512 Hash is a secure hashing algorithm and is not vulnerable to attacks. However, using weak passwords or hashing algorithms can make the system vulnerable to password cracking attacks.
Conclusion
SHA512 Hash is a powerful hashing algorithm that provides secure communication and data privacy. It generates a fixed-length hash value that ensures the integrity of messages and data transmitted over a network. By understanding the working of SHA512 Hash and its key features, developers can develop secure communication channels and protect digital assets.
