Introduction
In today’s world, data security is more critical than ever before. As a result, developers need to seek out the most effective and secure methods for protecting their data. One such tool is PGP Sign, a method for encrypting and signing communications using public and private keys. This article will explore what PGP Sign is, how it works, its features, and some useful scenarios for developers.
What is PGP Sign?
PGP Sign stands for Pretty Good Privacy, which is a data encryption and decryption software. It uses public-key cryptography, which means that two keys are involved in securing communications. A public key is used to encrypt the message, and a private key is used to decrypt it. This makes it a secure method of communication since only the intended recipient can decrypt the message.
How PGP Sign works
Here’s a brief overview of how PGP Sign works:
- A user generates a pair of keys: one private and one public.
- The user shares their public key with others, who can use it to encrypt messages to them.
- The user keeps their private key secure and uses it to decrypt messages sent to them.
To sign a message with PGP Sign, the user hashes the message with a secure algorithm and then encrypts the resulting hash with their private key. The recipient can then use the sender’s public key to decrypt the hash and verify that the message hasn’t been tampered with.
PGP Sign features
Here are some key features of PGP Sign:
| Feature | Description |
|---|---|
| Authentication | PGP Sign provides a secure way to authenticate the sender of a message. |
| Confidentiality | PGP Sign ensures that only the intended recipient can read the message. |
| Integrity | PGP Sign guarantees that the message hasn’t been altered in transit. |
| Key management | PGP Sign makes it easy to generate, import, and export keys. |
| Cross-platform support | PGP Sign is available on several platforms, including Windows, Linux, and macOS. |
Scenarios for developers
As a developer, there are several scenarios where PGP Sign can be useful, such as:
- Signing and verifying software releases
- Securing communication between team members
- Protecting sensitive data sent over email or instant messaging
Misconceptions and FAQs
Misconception: PGP Sign is only useful for encrypting emails. Fact: PGP Sign can be used to encrypt any kind of communication, including instant messages, software releases, and backups.
FAQ: How can I generate a set of PGP keys? Answer: You can use a tool like GnuPG to generate a pair of keys. Alternatively, you can use PGP Sign tool in He3 Toolbox (https://t.he3app.com?uyzq) easily.
FAQ: What if I lose my private key? Answer: Your private key is critical to decrypting messages sent to you. If you lose it, you won’t be able to read any messages that were encrypted using it. Be sure to back up your private key and store it securely.
Conclusion
PGP Sign is a powerful tool for securing your data with encryption and cryptography. Whether you’re a developer looking to protect sensitive communications or a business looking to secure its data, PGP Sign can provide the security you need. To learn more about PGP Sign, check out the Wikipedia page on Pretty Good Privacy.
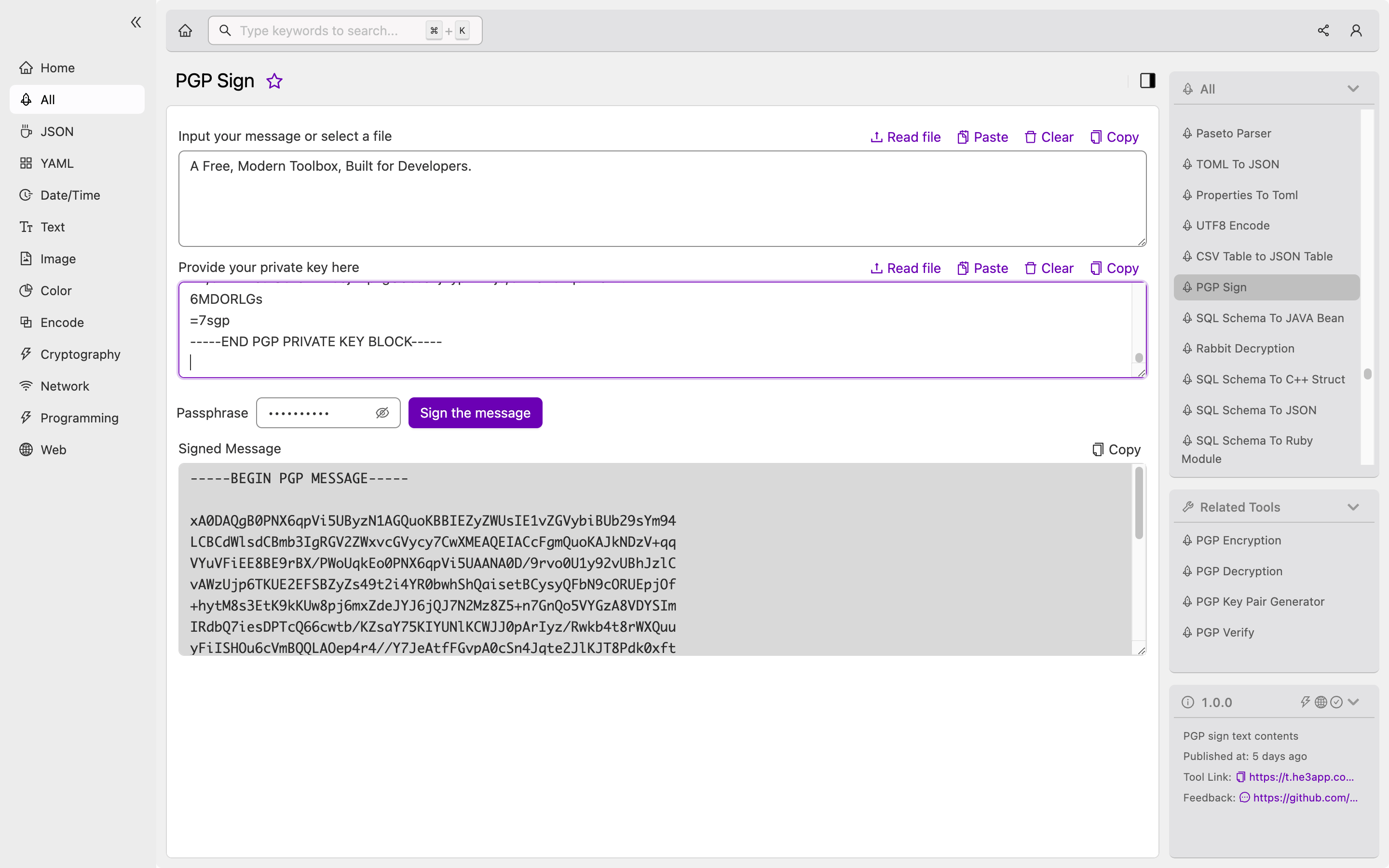
Or you can use PGP Sign tool in He3 Toolbox (https://t.he3app.com?uyzq) easily.
