Rabbit Decryption: Understanding the Concept and How It Works
In the world of security, encryption and decryption are critical processes to ensure data protection. One of the widely-used encryption algorithms is the Rabbit Decryption, a symmetric key stream cipher. This article aims to explain the concept of Rabbit Decryption and how it works.
How It Works
Rabbit Decryption is a type of synchronous stream cipher, meaning it encrypts and decrypts data one bit at a time. It uses a 128-bit secret key to generate a pseudo-random stream of bits, which serves as the keystream used in encrypting and decrypting plain text. The cipher generated by Rabbit is suitable for use in software and hardware.
One of the essential components of Rabbit Decryption is the state, which is the information that the cipher needs to generate the keystream. The state comprises eight 32-bit words, a carry bit, and a counter. The counter stores the position of the current keystream in the state.
The following are the steps on how Rabbit Decryption works:
- Initialize the state with the secret key and a 64-bit initialization vector (IV).
- Generate the keystream by processing the state with the counter.
- XOR the keystream with the plain text to encrypt or the cipher text to decrypt.
Sample Code
In Python, you can use the PyCryptodome library to use Rabbit Decryption. Here’s a sample code for Rabbit encryption:
from Crypto.Cipher import Rabbit
from Crypto.Random import get_random_bytes
key = get_random_bytes(16)
cipher = Rabbit.new(key)
msg = b'This is a sample message'
ciphertext = cipher.encrypt(msg)
print(ciphertext.hex())And for Rabbit decryption:
key = get_random_bytes(16)
cipher = Rabbit.new(key)
ciphertext = b'2e1559e98a1d2e2b287e506a0150b747'
msg = cipher.decrypt(bytes.fromhex(ciphertext))
print(msg.decode())Scenarios
Developers can use Rabbit Decryption in the following situations:
- Secure communication: Rabbit Decryption is useful in securing communication channels between two parties. Both parties must have the same secret key to encrypt and decrypt messages.
- File encryption: Developers can use Rabbit Decryption to encrypt files to protect them from unauthorized access. They can decrypt the files using the same key.
Key Features
Rabbit Decryption has the following key features:
| Features | Description |
|---|---|
| Security | Rabbit Decryption is a secure encryption algorithm that uses a secret key to generate a pseudo-random keystream. |
| Speed | Rabbit Decryption is an efficient stream cipher suitable for use in software and hardware. |
| Simplicity | Rabbit Decryption is easy to understand and implement, making it an ideal encryption algorithm for developers. |
Misconceptions and FAQs
1. Is Rabbit Decryption vulnerable to attacks?
Rabbit Decryption is a secure encryption algorithm and has not been found to have any significant weaknesses or vulnerabilities. However, like any encryption algorithm, it is susceptible to brute-force attacks if the key is too weak.
2. Can I use Rabbit Decryption on any platform?
Yes, Rabbit Decryption is suitable for use in software and hardware platforms. Developers can implement it on any programming language that supports it.
3. What is the difference between Rabbit Decryption and other stream ciphers?
Rabbit Decryption is a type of synchronous stream cipher that generates a 128-bit keystream. It is faster than most stream ciphers, making it efficient and suitable for use in software and hardware.
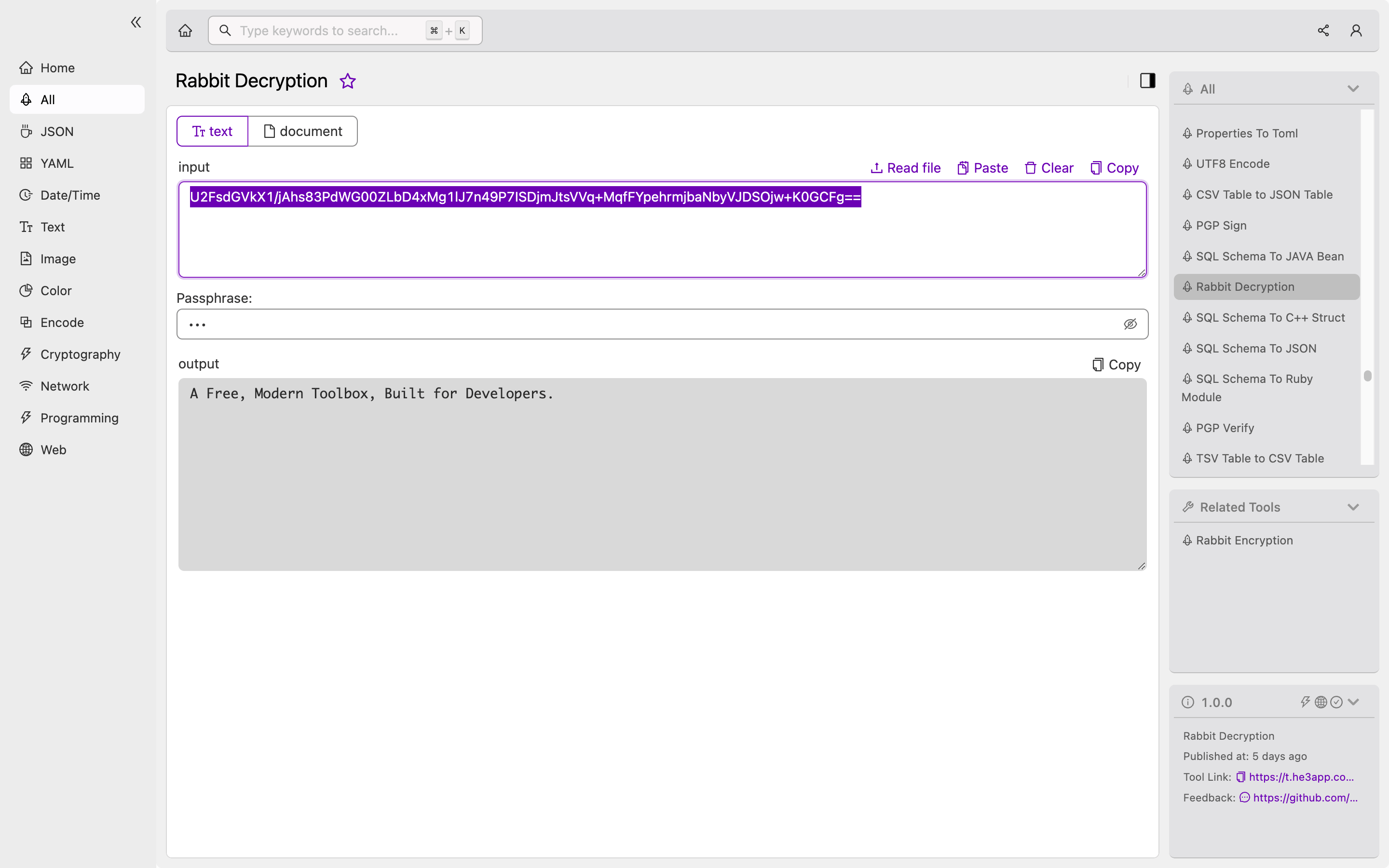
How to
Developers can use Rabbit Decryption tool in He3 Toolbox (https://t.he3app.com?d5sw) easily.
Conclusion
In conclusion, Rabbit Decryption is a secure and efficient symmetric key stream cipher that developers can use in securing data. It generates a pseudo-random keystream from a secret key, making it suitable for use in software and hardware platforms. By understanding Rabbit Decryption’s concept and how it works, developers can implement it to protect data from unauthorized access.
