Introduction
Developers working on applications, software, and hardware often need to ensure that the data transmitted between different systems or devices is accurate and free of errors. To achieve this, they use CRC16CCITT Hash to detect and prevent any errors or inconsistencies during transmission. CRC16CCITT Hash is an error-detection tool that verifies the integrity of data and ensures it remains unchanged during transmission.
How CRC16CCITT Hash Works
CRC16CCITT Hash works by computing a unique checksum for a given dataset using a hashing algorithm. The hashing algorithm then creates a fixed-length output called a digest or hash code, which is used to verify the data’s integrity. The unique checksum is compared to the original value to detect any errors that may have occurred.
To calculate the CRC16CCITT Hash, the algorithm splits the input data into fixed-sized blocks and generates a checksum for each block. The checksums are then combined to produce the final CRC16CCITT Hash output. The resulting hash code is a fixed-length value that serves as a unique identifier for the input data.
Here is an example of a CRC16CCITT Hash calculation using Python code:
import binascii
def crc16_ccitt(data):
crc = 0xFFFF
for byte in data:
crc = ((crc >> 8) & 0xFF) | ((crc << 8) & 0xFFFF)
crc ^= byte
crc ^= (crc & 0xFF) >> 4
crc ^= (crc << 8) << 4
crc ^= ((crc & 0xFF) << 4) << 1
return crc
data = b'Hello, World!'
crc = crc16_ccitt(data)
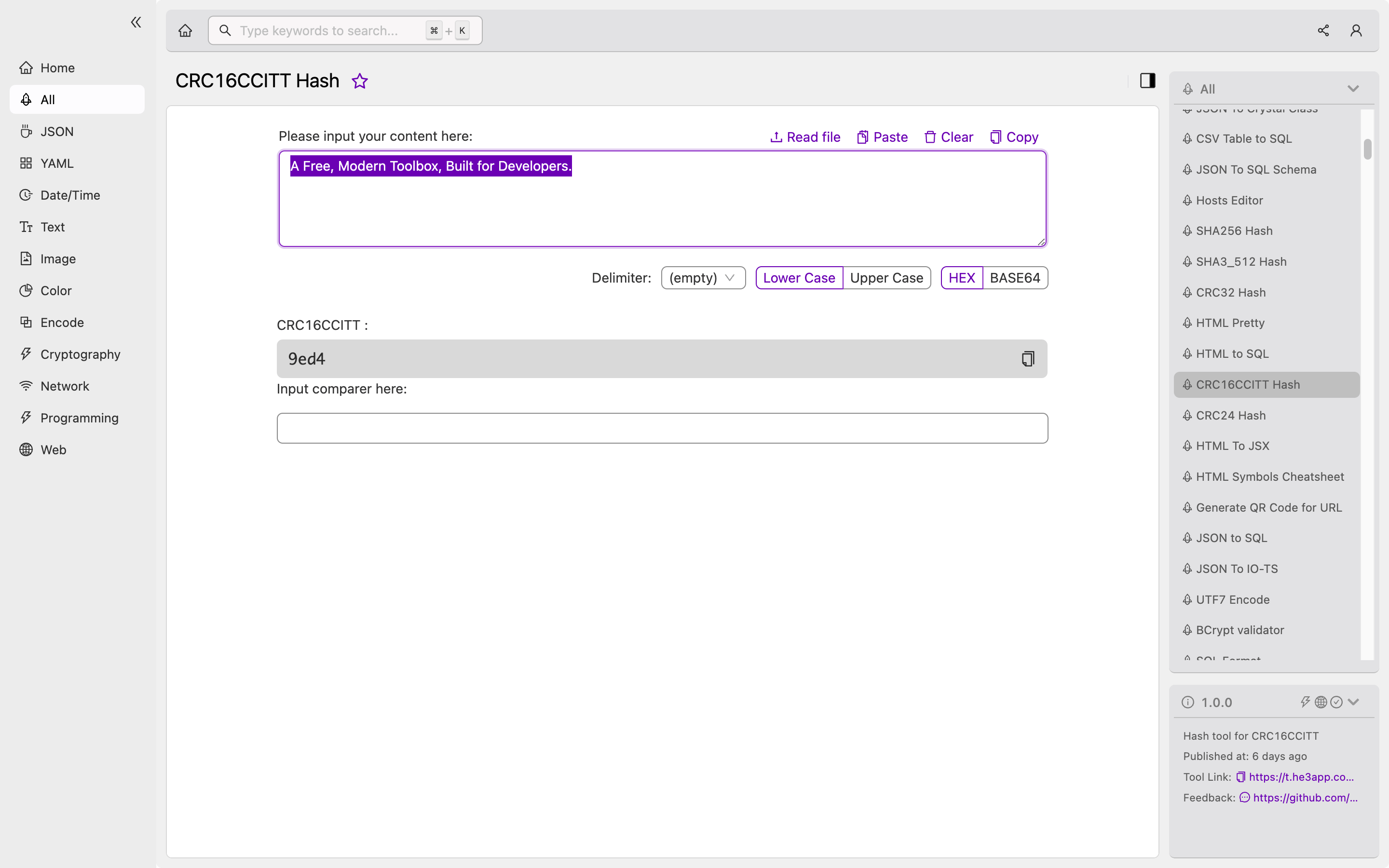
print(hex(crc))Or you can use CRC16CCITT Hash tool in He3 Toolbox (https://t.he3app.com?ygan ) easily.
Scenarios for Developers
Developers use CRC16CCITT Hash in applications and software that require data to be transmitted over unreliable channels, such as the internet or wireless networks. CRC16CCITT Hash serves as an error detection tool that ensures the transmitted data remains intact, and any errors are detected and corrected.
Developers also use CRC16CCITT Hash in hardware applications, such as microcontrollers, to verify the integrity of data stored in memory or transmitted over communication interfaces.
Key Features
Below are the key features of CRC16CCITT Hash:
- Fast and efficient computation of checksums
- Widely supported in different programming languages and hardware platforms
- Provides high reliability for error detection and correction
- Simple and easy to implement
Misconceptions and FAQs
Misconception: CRC16CCITT Hash guarantees data privacy
CRC16CCITT Hash provides error detection and correction but does not prevent any unauthorized access to the data. It is not a tool for ensuring data privacy, and additional cryptographic techniques are required to achieve this.
FAQ 1: What is the difference between CRC16 and CRC16CCITT Hash?
CRC16 and CRC16CCITT Hash generate different checksums because they use different polynomial algorithms. CRC16CCITT Hash uses an algorithm that is more widely used and provides better error detection capabilities than CRC16.
FAQ 2: What happens if the CRC16CCITT Hash value does not match the original data?
If the CRC16CCITT Hash value does not match the original data, it indicates that an error occurred during the transmission of the data. The receiver can request the transmitter to resend the data to ensure its accuracy.
Conclusion
In conclusion, CRC16CCITT Hash is a critical tool for developers in ensuring the integrity of data transmitted or stored to prevent any errors or inconsistencies. Its key features include fast and efficient computation, simplicity, and high error detection reliability. Developers can use CRC16CCITT Hash in various scenarios, including hardware and software applications, to ensure data transmission remains unchanged. To learn more about CRC16CCITT Hash, please visit https://en.wikipedia.org/wiki/Cyclic_redundancy_check.
