Introduction
As a developer, you may be familiar with the concept of hash functions, which generate a fixed-size output from an input data of any length. Hash functions are widely used to ensure data integrity and provide error detection in various scenarios. One such hash function is CRC24 Hash, which uses a cyclic redundancy check (CRC) algorithm to generate a 24-bit output. In this article, we’ll dive into the details of CRC24 Hash, how it works, and how you can use it in your development projects.
What Is CRC24 Hash?
CRC24 Hash is a hash function that uses the CRC algorithm to generate a 24-bit output. The CRC algorithm is a type of checksum that detects errors in digital data transmission, such as corrupted or altered data. The CRC algorithm works by dividing the input data into a series of equal-length chunks, performing a series of bitwise operations, and generating a remainder that represents the checksum.
CRC24 Hash extends the basic CRC algorithm by using a polynomial function with a degree of 24. The polynomial function is used to generate a binary sequence that represents the input data. The binary sequence is then divided into equal-length chunks, and the CRC algorithm is applied to each chunk to generate a 24-bit output. The 24 bits represent the remainder of the polynomial division.
How Does CRC24 Hash Work?
CRC24 Hash works by performing a series of bitwise operations on the input data, using a polynomial function to generate a binary sequence, and applying the CRC algorithm to each chunk of the binary sequence to generate a 24-bit output. The bitwise operations involve XORing the input byte with a predefined value and shifting the result to the left. The polynomial function is represented in binary form and is XORed with each byte of the data to generate the binary sequence.
To calculate the CRC24 Hash of a piece of data, you need to follow these steps:
- Initialize a 24-bit value to a predefined constant value.
- Iterate through each byte of the input data, performing the following operations:
- XOR the byte with the high byte of the 24-bit value.
- Shift the result to the left by 8 bits.
- XOR the result with the low byte of the 24-bit value.
- Look up the 24-bit value in a predefined lookup table and XOR the result with the 24-bit value.
- Return the 24-bit value.
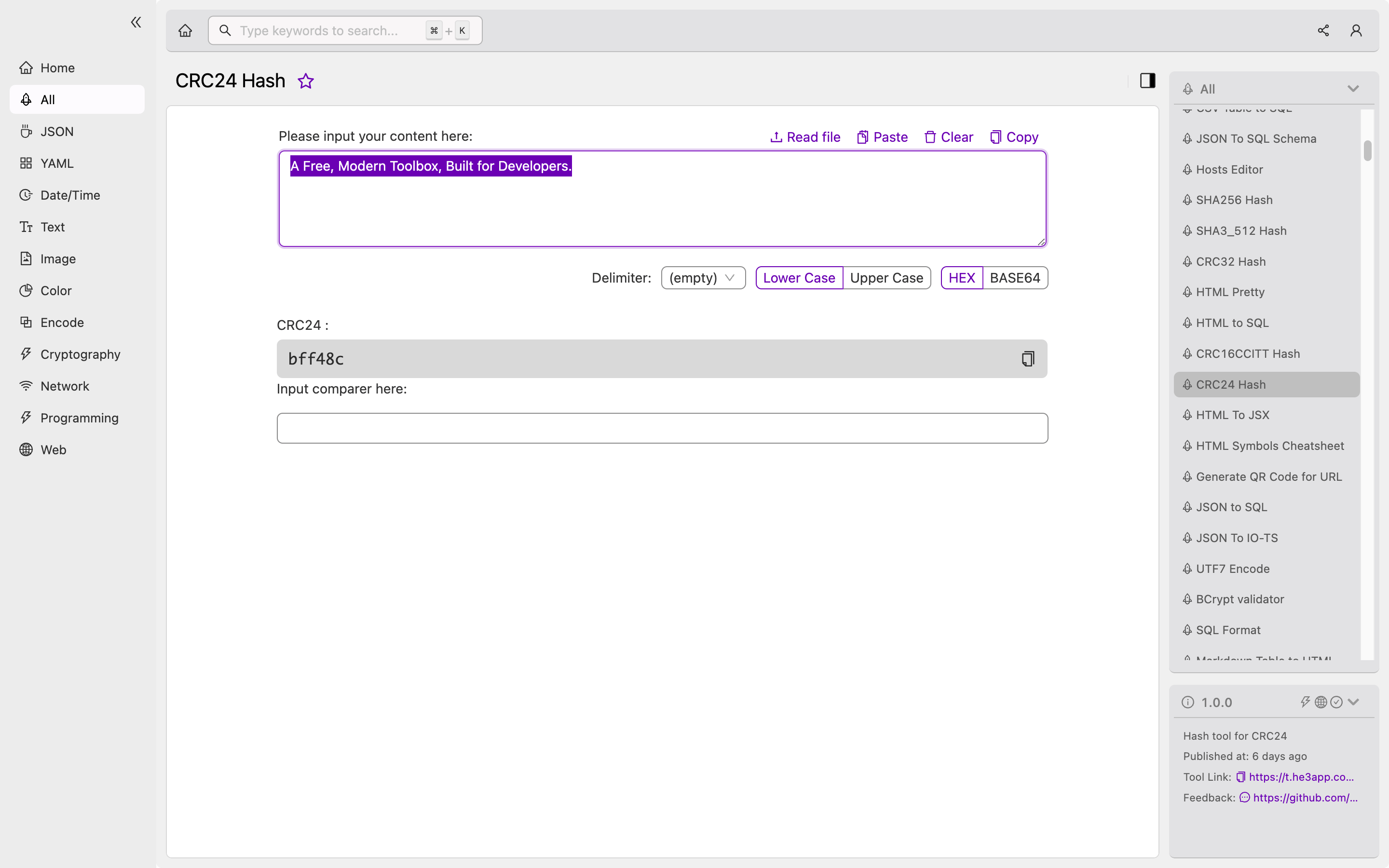
Or you can use CRC24 Hash tool in He3 Toolbox (https://t.he3app.com?gmlk ) easily.
Scenarios for Using CRC24 Hash
CRC24 Hash is commonly used for error detection and data integrity in various scenarios, such as:
- Network protocols: CRC24 Hash can be used to ensure the integrity of data transmitted over a network, such as packets in a TCP/IP or Ethernet network.
- Disk storage: CRC24 Hash can be used to detect errors in data stored on a disk, such as in the File Allocation Table (FAT) format.
- Cryptography: CRC24 Hash can be used as a component of cryptographic systems, such as in digital signatures or message authentication codes.
Key Features of CRC24 Hash
Here are some of the key features of CRC24 Hash:
- Provides error detection for data transmission and storage scenarios.
- Generates a fixed-size 24-bit output.
- Relatively fast and efficient to compute.
- Works well for data with a high degree of randomness.
- Is not suitable for cryptographic purposes, as it is vulnerable to collision attacks.
Misconceptions About CRC24 Hash
There are several misconceptions about CRC24 Hash that you should be aware of. Here are a few:
- CRC24 Hash is not a cryptographic hash function, as it is vulnerable to collision attacks.
- CRC24 Hash is not a replacement for other hash functions, such as SHA-256, as it has a limited output size and is not suitable for all scenarios.
- CRC24 Hash does not provide encryption, as it only provides error detection and data integrity.
Frequently Asked Questions
Q: Can CRC24 Hash be reversed to obtain the original data? A: No, CRC24 Hash is a one-way function, which means that it cannot be reversed to obtain the original data.
Q: How does CRC24 Hash compare to other hash functions, such as SHA-256? A: CRC24 Hash has a smaller output size compared to SHA-256 and is not suitable for all scenarios. SHA-256 is a cryptographic hash function that provides greater security and resistance to collision attacks.
Q: How can I implement CRC24 Hash in my development project? A: You can use a CRC24 Hash library or implement the algorithm yourself using the guidelines provided in this article.
Conclusion
In conclusion, CRC24 Hash is a hash function that provides error detection and data integrity in various scenarios. It uses the CRC algorithm to generate a 24-bit output from an input data of any length. While not suitable for cryptographic purposes, CRC24 Hash is efficient and fast to compute, making it an ideal choice for scenarios that require error detection and data integrity. You can learn more about CRC24 Hash on Wikipedia.
