If you’re a developer working with cryptography, you’ve likely heard of the HAS160 Hash, a popular secure hash function used for generating message digests and encryption purposes. In this article, we’ll provide a comprehensive guide for developers looking to understand the concept and capabilities of HAS160 Hash, its key features, scenarios of use, misconceptions, and FAQs.
Understanding HAS160 Hash
HAS160 Hash is a 160-bit secure cryptographic hash function, derived from the SHA-1 algorithm, designed and implemented in South Korea. It’s used for message digest and encryption purposes, and it’s a popular choice due to its high security and speed.
The hash function takes an input message of any length and generates a fixed-size output hash, as such it’s a one-way function that cannot be reversed. Its security relies on the avalanche effect, meaning that a small change in the input message produces a completely different output hash. Furthermore, it’s computationally infeasible to find the original input message given the output hash.
Key Features Table
The following table outlines the key features of HAS160 Hash:
| Key Feature | Description |
|---|---|
| Hash size | 160 bits |
| Block size | 512 bits |
| Rounds | 80 |
| Cryptographic | One-way function, avalanche effect, collision resistant |
Scenarios of Use
HAS160 Hash is a popular choice for developers involved in cryptography and security applications, such as:
- Digital signatures
- Authentication
- Message authentication codes
- Key derivation
- Password storage
How to Use HAS160 Hash
To use HAS160 Hash, you can use a variety of programming languages, such as C, C++, Python, Java, and more. Here’s an example Python code snippet for computing the hash of a message:
import hashlib
message = b"Hello World"
hash_object = hashlib.has160(message)
hash_hex = hash_object.hexdigest()
print("Message:", message)
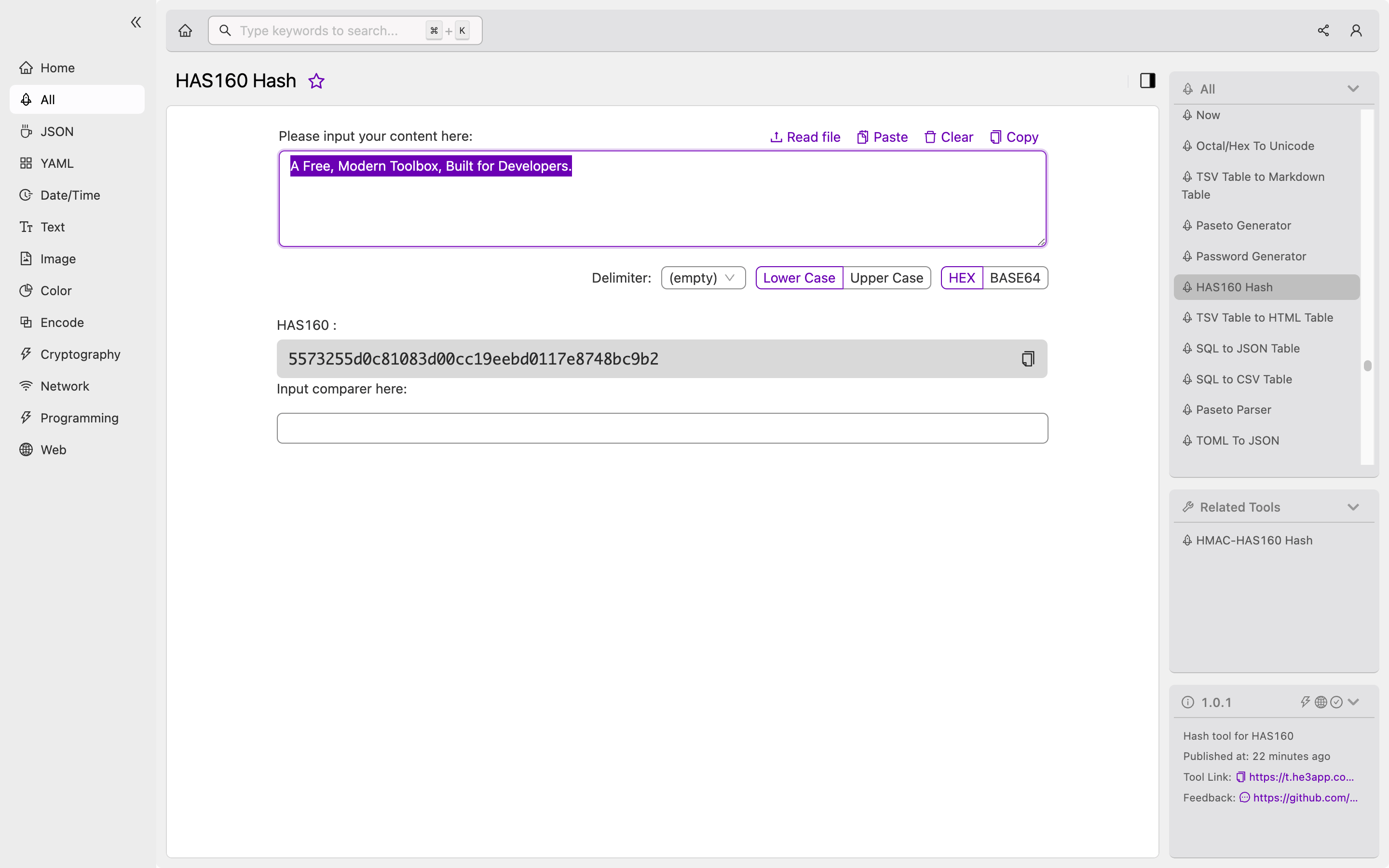
print("Hash (hex):", hash_hex)Or you can use HAS160 Hash tool in He3 Toolbox (https://t.he3app.com?cr6s ) easily.
Misconceptions and FAQs
Misconception: HAS160 Hash is not secure
While SHA-1, the parent algorithm of HAS160 Hash, is known to have some vulnerabilities, HAS160 Hash is still considered a secure hash function. It’s resistant to collision attacks and has been widely studied and analyzed by the cryptographic community.
FAQ 1: Why is HAS160 Hash not used as much as other hash functions?
HAS160 Hash is not as widely used as other hash functions, such as SHA-256 or SHA-3, due to its smaller block size and lower adoption rate. However, it’s still a secure and efficient choice for many cryptographic applications.
FAQ 2: Can HAS160 Hash be used for encryption?
While HAS160 Hash can generate a fixed-size hash of a message, it cannot be directly used for encryption purposes. However, it can be used in combination with other cryptographic algorithms, such as symmetric encryption or digital signatures, for secure message transmission and storage.
Conclusion
HAS160 Hash is a popular and secure hash function used for generating message digests and encryption purposes. Its high security and speed make it an attractive choice for developers involved in cryptography and security applications. We hope this guide has provided you with a better understanding of the concept and capabilities of HAS160 Hash.
For further reading, check out the following resources:
