Introduction
JSON Web Token (JWT) is a popular open standard for token-based authentication and authorization. It is used extensively in web applications as a secure way to transmit information between two parties. JWTs are compact, URL-safe, and digitally signed, making them suitable for use in a wide range of scenarios. However, decoding or parsing JWTs can be a challenging task for developers. JWT Parser is a powerful tool that simplifies the process of decoding and encoding JWTs.
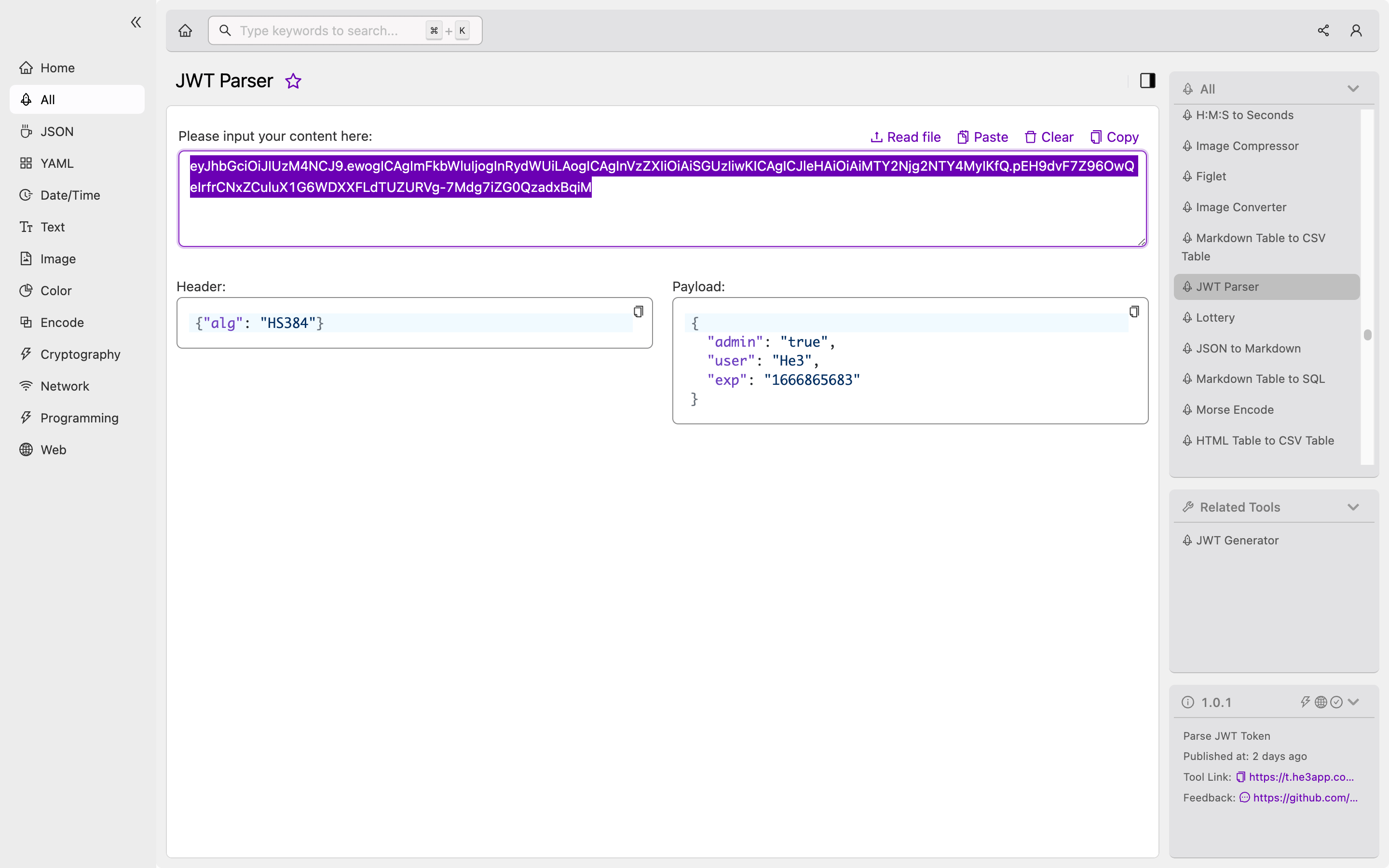
Understanding JWT Parser
JWT Parser is a tool that helps developers parse and manipulate JSON Web Tokens. It provides a simple interface to decode JWTs and extract their contents. This tool can be used to verify the authenticity of a JWT, inspect its contents, and generate new JWTs. JWT Parser supports all JWT-related algorithms, including HMAC SHA256, RSA SHA256, and ECDSA.
The tool is designed with ease of use in mind, and it allows developers to view the claims contained within a JWT in a user-friendly manner. It also supports base64 decoding of JWTs, allowing developers to view the contents of the token in plain text. The tool supports both encoded and decoded JWTs.
How to use JWT Parser
Developers can use the JWT Parser tool in He3 Toolbox (https://t.he3app.com?ukle ) easily. Or, they can use the following code snippets in Python to parse a JWT:
import jwt
token = jwt.decode(my_token, verify=False)Here, my_token is the JWT that needs to be parsed. The verify parameter is set to False to disable signature verification.
Key Features
The key features of JWT Parser are as follows:
| Feature | Description |
|---|---|
| Support for all JWT-related algorithms | JWT Parser supports HMAC SHA256, RSA SHA256, and ECDSA. |
| User-friendly interface | JWT Parser provides a simple interface to decode and encode JWTs. |
| Support for base64 decoding of JWTs | Developers can view the contents of a JWT in plain text. |
| Supports both encoded and decoded JWTs | Developers can work with both encoded and decoded JWTs. |
Scenarios for Developers
JWT Parser can be used in various scenarios, including:
- Verifying the authenticity of a JWT
- Inspecting the claims of a JWT
- Generating new JWTs
- Debugging JWT-related issues
Misconceptions and FAQs
Misconceptions
JWTs are often confused with session tokens or cookies. While session tokens are stored on the server, JWTs are stored on the client-side. JWTs can be used for single sign-on (SSO) and can be shared between multiple parties.
FAQs
Q1. Can JWT Parser be used for encoding JWTs?
Yes, JWT Parser can be used to encode JWTs. Developers can simply enter the payload and select the appropriate algorithm to generate a new JWT.
Q2. What are the security considerations when using JWT Parser?
Developers need to ensure that the JWTs they are parsing or generating are valid and authentic. They should also ensure that the private keys and secrets used for encoding or decoding JWTs are kept secure.
Q3. How can JWT Parser help in debugging JWT-related issues?
Developers can use JWT Parser to verify the contents of a JWT, including its claims, signatures, and algorithms. This can help in identifying issues related to the JWT.
Conclusion
JWT Parser is a powerful tool that helps developers parse and manipulate JSON Web Tokens. It supports all JWT-related algorithms and provides a simple interface to decode and encode JWTs. Developers can use JWT Parser to verify the authenticity of a JWT, inspect its contents, and generate new JWTs.
References:
