Introduction
In the world of cryptography, hash functions are vital tools that enable data security and integrity. One such hash function is Keccak512, which is a member of the Secure Hash Algorithm 3 (SHA-3) family. Keccak512 is based on the sponge construction paradigm, which is a versatile and secure framework for hash functions. In this article, we will delve into the concept and working of Keccak512 hash and explore its key features and applications.
Understanding Keccak512 Hash
Keccak512 hash is a one-way function that accepts a message of arbitrary length and outputs a 512-bit digest. This digest is unique to the input message, and any modification to the message will result in a completely different digest. Keccak512 hash is a highly secure and collision-resistant function, which means that it is practically impossible to find two different messages that produce the same digest.
Keccak512 hash is built on the sponge construction paradigm, which is a type of hash function that absorbs input data and compresses it into fixed-sized blocks. The sponge construction consists of two main phases: an absorb phase, where the input data is absorbed, and a squeeze phase, where the output digest is generated. During the absorb phase, the input data is XOR-ed with a padded version of the internal state of the hash function. The resulting state is then transformed using a permutation function. This process is repeated until all the input data is absorbed. During the squeeze phase, the internal state is repeatedly transformed and truncated to generate the output digest.
Key Features of Keccak512 Hash
The following table summarizes the key features of Keccak512 hash:
| Feature | Description |
|---|---|
| Digest Size | 512 bits |
| Block Size | 576 bits |
| Security | Highly secure and collision-resistant |
| Performance | Fast and efficient on modern hardware |
| Padding | Customizable padding schemes for input data |
| Applications | Cryptography, digital signatures, blockchain, password storage |
Scenarios of Use
Keccak512 hash can be used in a wide range of scenarios where data security and integrity are crucial. Some examples include:
- Cryptography: Keccak512 hash is commonly used in cryptographic applications such as key generation, message authentication, and encryption.
- Digital Signatures: Keccak512 hash is used to generate digital signatures that can be used for user authentication and data verification.
- Blockchain: Keccak512 hash is used in many blockchain implementations to secure transactions and blocks.
- Password Storage: Keccak512 hash is used to securely store passwords in databases and authenticate user logins.
How to Use Keccak512 Hash
Keccak512 hash can be implemented in various programming languages, including C++, Python, and Java. Here is an example of how to use Keccak512 hash in Python:
import hashlib
message = b'hello world'
hash_object = hashlib.sha3_512()
hash_object.update(message)
digest = hash_object.digest()
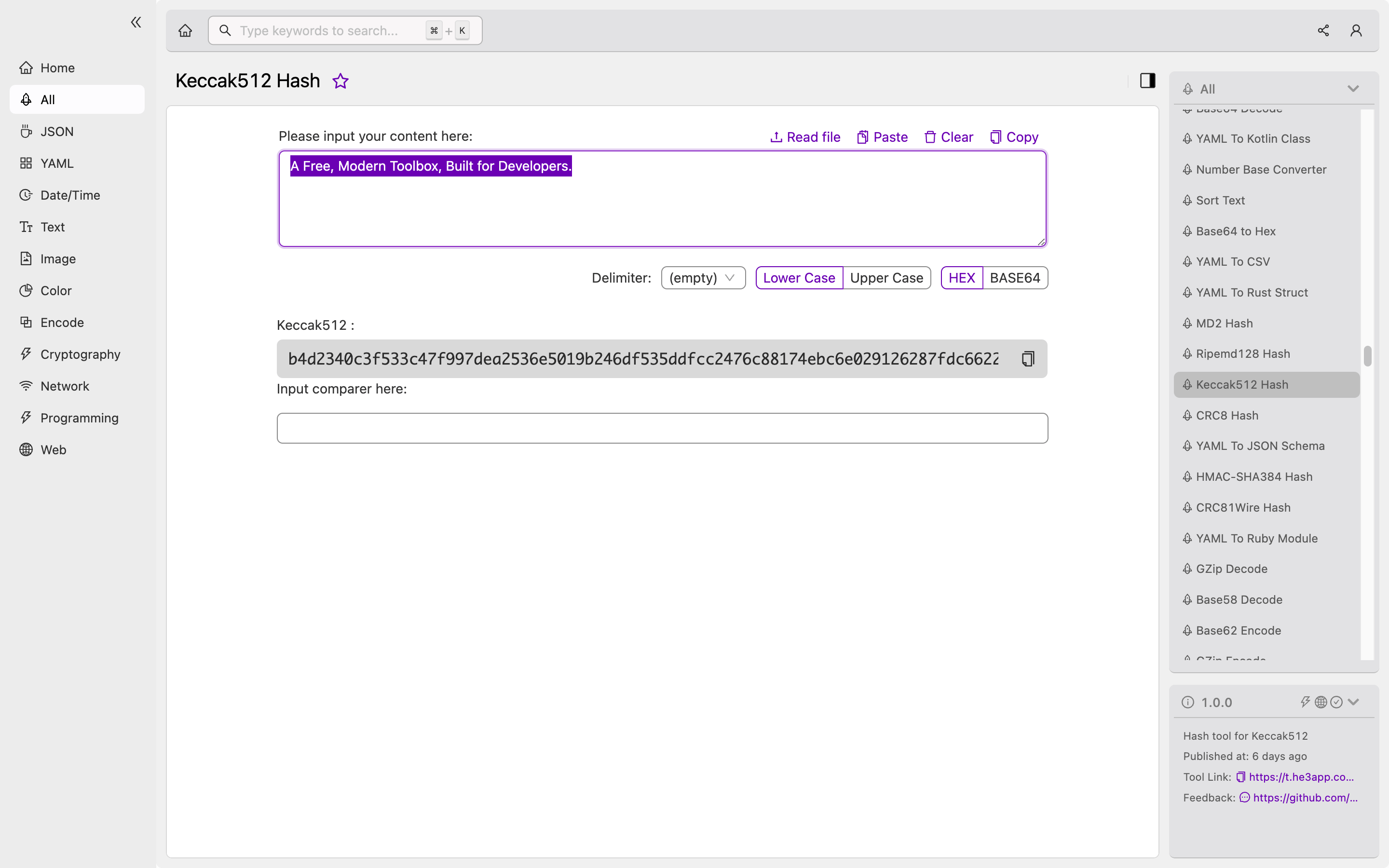
print(digest.hex())Or you can use Keccak512 Hash tool in He3 Toolbox (https://t.he3app.com?7wum ) easily.
Misconceptions and FAQs
Is Keccak512 hash the same as SHA-3?
Keccak512 hash is a member of the SHA-3 family of hash functions. However, SHA-3 encompasses a range of hash functions of different sizes, including Keccak512, Keccak256, and Keccak224.
Can Keccak512 hash be reversed?
Keccak512 hash is a one-way function, which means that it is practically impossible to reverse the output digest to obtain the original message.
Conclusion
Keccak512 hash is a highly secure and efficient hash function that is widely used in cryptography, digital signatures, blockchain, and other applications. With its collision-resistant and one-way properties, Keccak512 hash is a valuable tool for securing data in your applications. For more information on Keccak512 hash and SHA-3, check out the following links:
