Introduction
In today’s digital world, data is transmitted and stored in various ways. The security of this data is essential to prevent unauthorized access and ensure data integrity. MD5 Hash is one of the widely used cryptographic algorithms that ensures data integrity, authentication, and non-repudiation. In this guide, we will take a closer look at MD5 Hash and how it works.
What is MD5 Hash?
MD5 Hash is a message digest algorithm that generates a fixed-size, 128-bit hash value from a variable-length input message. This hash value is unique to the input message, and any change in the input message results in a completely different hash value. MD5 Hash is a one-way function, which means that it is not possible to generate the original message from the hash value.
MD5 Hash was designed by Ronald Rivest in 1991 as a successor to MD4 Hash, which had some vulnerabilities. However, over the years, several security weaknesses have been discovered in MD5 Hash as well, and it is no longer recommended for cryptographic purposes in most cases.
How does MD5 Hash work?
MD5 Hash uses a series of logical operations to process the input message in blocks of 512 bits. The input message is padded to a multiple of 512 bits to ensure that the last block is less than or equal to 512 bits. The padded message is then divided into 16 32-bit words and processed through four rounds of operations. These operations include bitwise logical functions such as AND, OR, and XOR, as well as rotations and additions modulo 2^32.
The output of each round is combined with the result of the previous round using a set of fixed functions. Finally, the output from the fourth round is the resulting 128-bit hash value.
Key Features of MD5 Hash
| Features | Description |
|---|---|
| Message Digest Algorithm | Generates a unique fixed-size hash value from a variable-length input message. |
| One-way Function | It’s impossible to generate the original message from the hash value. |
| Fast and Efficient | It’s faster and less computationally intensive than other hash algorithms. |
| Widely Supported | Supported by most programming languages and operating systems. |
Scenarios of using MD5 Hash for Developers
MD5 Hash can be used in various scenarios by developers, including:
- Ensuring data integrity: MD5 Hash can be used to verify that the data has not been tampered with during transmission or storage.
- Password hashing: MD5 Hash can be used to store password hashes in databases to prevent plaintext passwords from being stolen.
- Digital signatures: MD5 Hash can be used to sign digital documents and ensure non-repudiation.
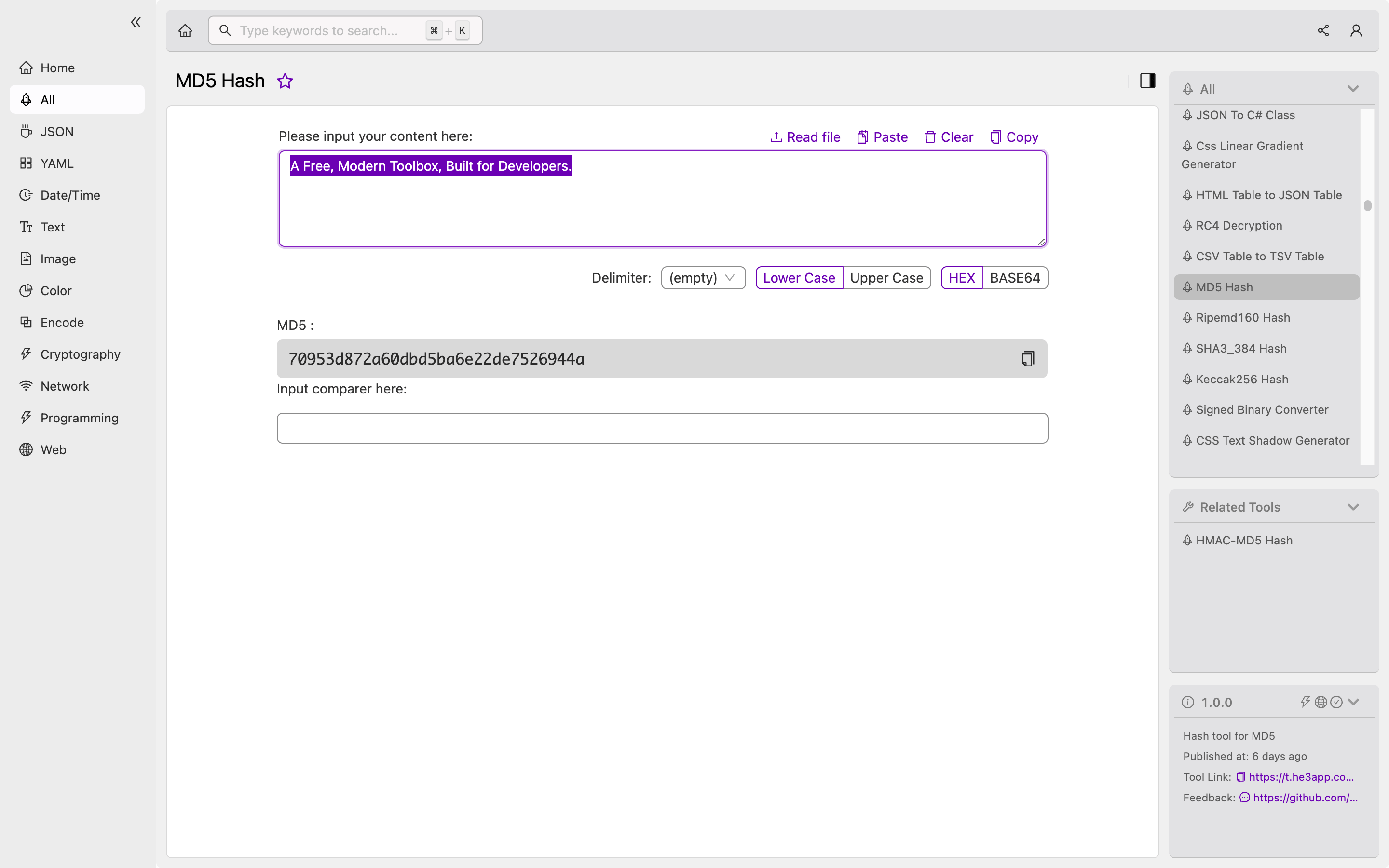
Or you can use MD5 Hash tool in He3 Toolbox (https://t.he3app.com?if34 ) easily.
Misconceptions and FAQs
Misconception: MD5 Hash is unbreakable
Although it’s true that it’s impossible to generate the original message from the hash value, there are several ways to compromise MD5 Hash’s integrity. Several attacks have been discovered over the years that can generate MD5 Hash collisions, which means that two different messages can have the same hash value. Therefore, MD5 Hash is no longer recommended for cryptographic purposes in most cases.
FAQ 1: Is MD5 Hash still secure?
No, MD5 Hash is no longer considered secure for cryptographic purposes. Several security weaknesses have been discovered in MD5 Hash over the years, and it’s recommended to use other hash algorithms such as SHA-256 or SHA-3 instead.
FAQ 2: Can MD5 Hash be reversed?
No, it’s impossible to generate the original message from the MD5 Hash value since it’s a one-way function.
Conclusion
In conclusion, MD5 Hash is a widely used algorithm for message digest that generates a unique hash value from a variable-length input message. Although it’s no longer considered secure for cryptographic purposes, it can still be used in various scenarios by developers to ensure data integrity and non-repudiation. As a developer, it’s essential to understand the concept and mechanism of MD5 Hash and use it wisely in appropriate situations.
References:
