If you are working with cryptography, security or data integrity, you might have come across the term hash function or message digest. Hash function is an algorithm that transforms an input or message - of any size - into a fixed-size output, typically a sequence of digits or letters known as the hash, digest or fingerprint. One such hash function is MD6_256 Hash, a secure, fast and efficient cryptographic hash function that produces a 256-bit hash value.
How MD6_256 Hash Works
MD6_256 Hash is a Merkle-Damgard hash function that uses a block size of 256 bits and can process messages of any length. It works by dividing the message into 256-bit blocks, padding the last block if needed, and processing each block using a compression function that iterates over a fixed number of rounds. The compression function combines the current state and the input block using the message schedule, an array of precomputed values derived from the input block. The final hash value is the concatenation of the output of the compression function for each block.
MD6_256 Hash has several desirable properties, including collision resistance, preimage resistance, and second preimage resistance. Collision resistance means it is computationally infeasible to find two different messages that produce the same hash value. Preimage resistance means it is computationally infeasible to find a message that produces a given hash value. Second preimage resistance means it is computationally infeasible to find a second message that produces the same hash value as a given message.
Scenarios for Developers
MD6_256 Hash has many applications in computer science and information security, including:
- Password storage and verification
- Digital signatures and authentication
- File integrity checking and verification
- Message authentication and verification
- Blockchain and cryptocurrency
- Data structures and algorithms
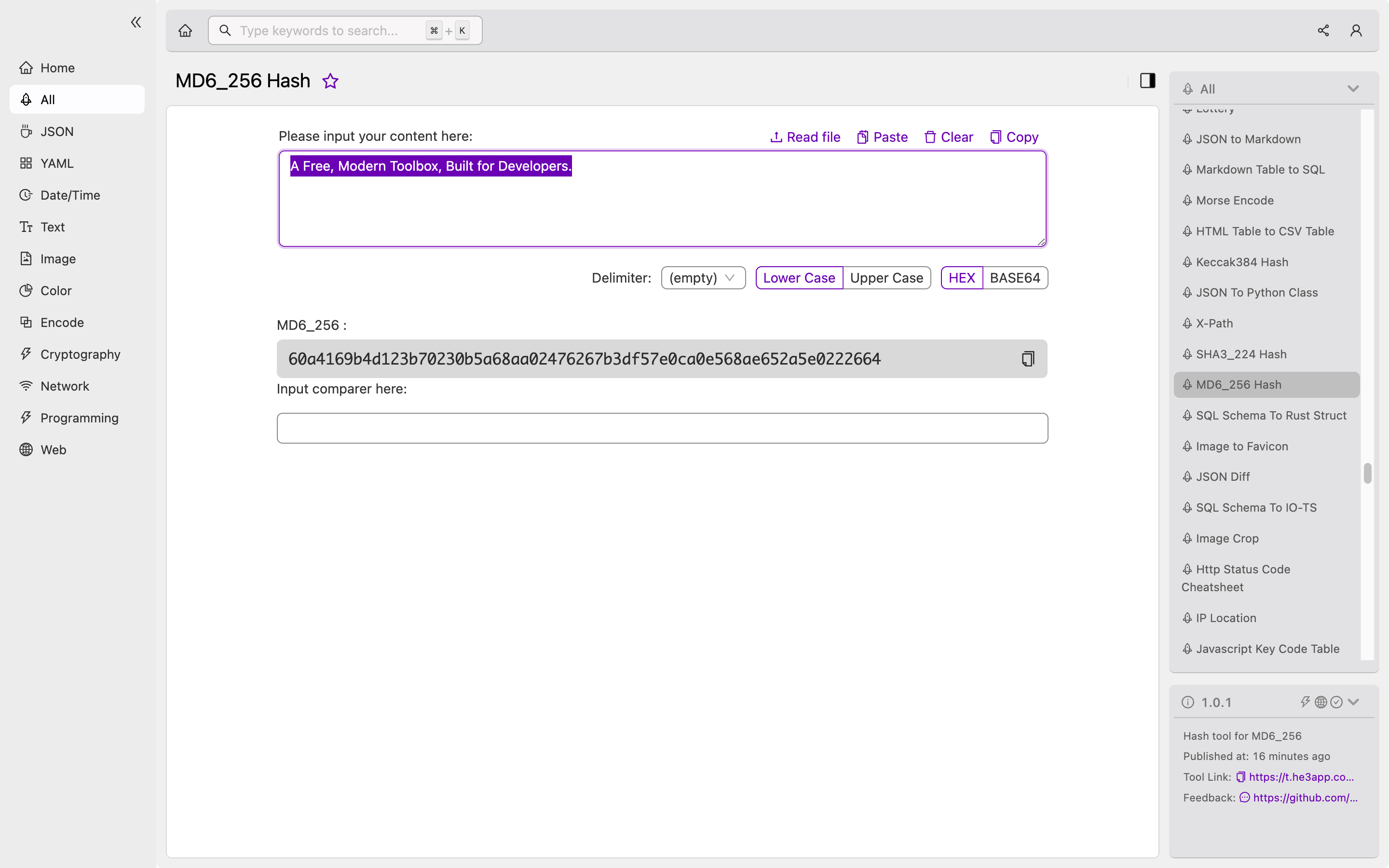
Developers can use MD6_256 Hash as a building block for implementing secure and trustworthy systems. They can also use existing libraries or tools that support MD6_256 Hash, such as OpenSSL, Python hashlib, and He3 Toolbox. For example, to hash a message using He3 Toolbox, developers can follow these steps:
- Load the message into He3 Toolbox
- Select MD6_256 Hash from the list of hash functions
- Click the “Hash” button to generate the hash value
Or you can use MD6_256 Hash tool in He3 Toolbox (https://t.he3app.com?xm0c ) easily.
Key Features of MD6_256 Hash
MD6_256 Hash has several key features that make it a popular choice for many applications, including:
- High security: MD6_256 Hash has a high degree of resistance against various attacks, including brute force, birthday, and length extension attacks.
- Fast and efficient: MD6_256 Hash is faster than many other secure hash functions, such as SHA-2 and SHA-3, while still maintaining a high level of security.
- Flexible block size: MD6_256 Hash supports any input message size and can efficiently process large messages.
- Incremental hashing: MD6_256 Hash can efficiently hash partial messages or large files without having to load the entire message into memory.
Misconceptions and FAQs
There are several misconceptions and FAQs about MD6_256 Hash that developers should be aware of, including:
- Is MD6_256 Hash a standardized hash function? No, MD6_256 Hash is not a standardized hash function and is not widely used in commercial or open-source software.
- Is MD6_256 Hash vulnerable to quantum attacks? The security of MD6_256 Hash against quantum attacks is not well understood, but it is expected to be less secure than hash functions that are based on post-quantum cryptography.
- How do I choose the right hash function for my application? The choice of hash function depends on many factors, such as the level of security required, the size and type of data to be hashed, and the performance and memory constraints of the system. Developers should consult with cryptography experts and use established standards and best practices when selecting a hash function.
In conclusion, MD6_256 Hash is a powerful and versatile cryptographic hash function that can be used for many applications. Developers should understand its concept, how it works, key features, and scenarios for use in their projects. They should also be aware of its limitations and use it alongside other security measures to ensure the integrity, confidentiality, and availability of their data.
References:
