In today’s digital age, data security and encryption have become crucial to safeguard sensitive information from cyber threats. Hash functions are widely used in cryptography to ensure the integrity and authenticity of data by generating a unique digital fingerprint that identifies a file or message. One such hash function that has gained popularity recently is MD6_384 Hash. In this article, we will explore everything you need to know about MD6_384 Hash, its features, scenarios, misconceptions, and FAQs.
What is MD6_384 Hash?
MD6_384 Hash is a cryptographic hash function designed to provide high security and data integrity. It is an extended version of the MD5 and SHA-2 hash functions, developed by Ronald L. Rivest in 2008. MD6_384 Hash uses a block cipher algorithm that converts an arbitrarily long message into a fixed-sized, 384-bit hash value. The algorithm is iterated a fixed number of times and modified based on the message length and other parameters, resulting in a unique hash value for each input.
How MD6_384 Hash Works
MD6_384 Hash is a complex algorithm that involves multiple steps, including key generation, message padding, and compression. The algorithm uses a Merkle-Damgard structure that breaks the input message into blocks, which are then iteratively processed with a compression function. The compression function is passed a message block, previous hash value, and a key value, resulting in a new hash value. The final hash value is obtained by concatenating the hash values of each block, resulting in a 384-bit output.
Scenarios for Developers
MD6_384 Hash is a popular choice for developers working in cybersecurity, data encryption, and digital signature fields. Some of the typical scenarios where developers use MD6_384 Hash include:
- Data integrity and authentication
- Digital signatures
- Password storage and verification
- Message authentication codes
- Secure communication protocols
Key Features of MD6_384 Hash
MD6_384 Hash comes with several key features that make it an ideal choice for data security and encryption. Some of the notable features include:
- 384-bit output for high security
- Merkle-Damgard structure for message padding
- Key generation for added security
- Fixed-length block processing for faster execution
- Customizable iterations and compression functions
Misconceptions And FAQs
Misconception 1: MD6_384 Hash is unbreakable
One of the most common misconceptions about MD6_384 Hash is that it is unbreakable. While MD6_384 Hash is a highly secure encryption mechanism, it is not entirely immune to attacks. Cryptographic hash functions are susceptible to collision attacks, where different messages generate the same hash value, compromising data integrity.
Misconception 2: MD6_384 Hash is a replacement for SHA-2
MD6_384 Hash is not a direct replacement for the widely used SHA-2 hash function. It is designed as an alternative that provides a higher level of security for specific scenarios, such as digital signatures and data encryption.
FAQ 1: Is MD6_384 Hash open-source?
Yes, MD6_384 Hash is an open-source cryptographic hash function.
FAQ 2: Can MD6_384 Hash be reversed?
No, MD6_384 Hash is a one-way hash function that cannot be reversed. The hash function generates a unique fingerprint for each input, but cannot retrieve the original message from the hash value.
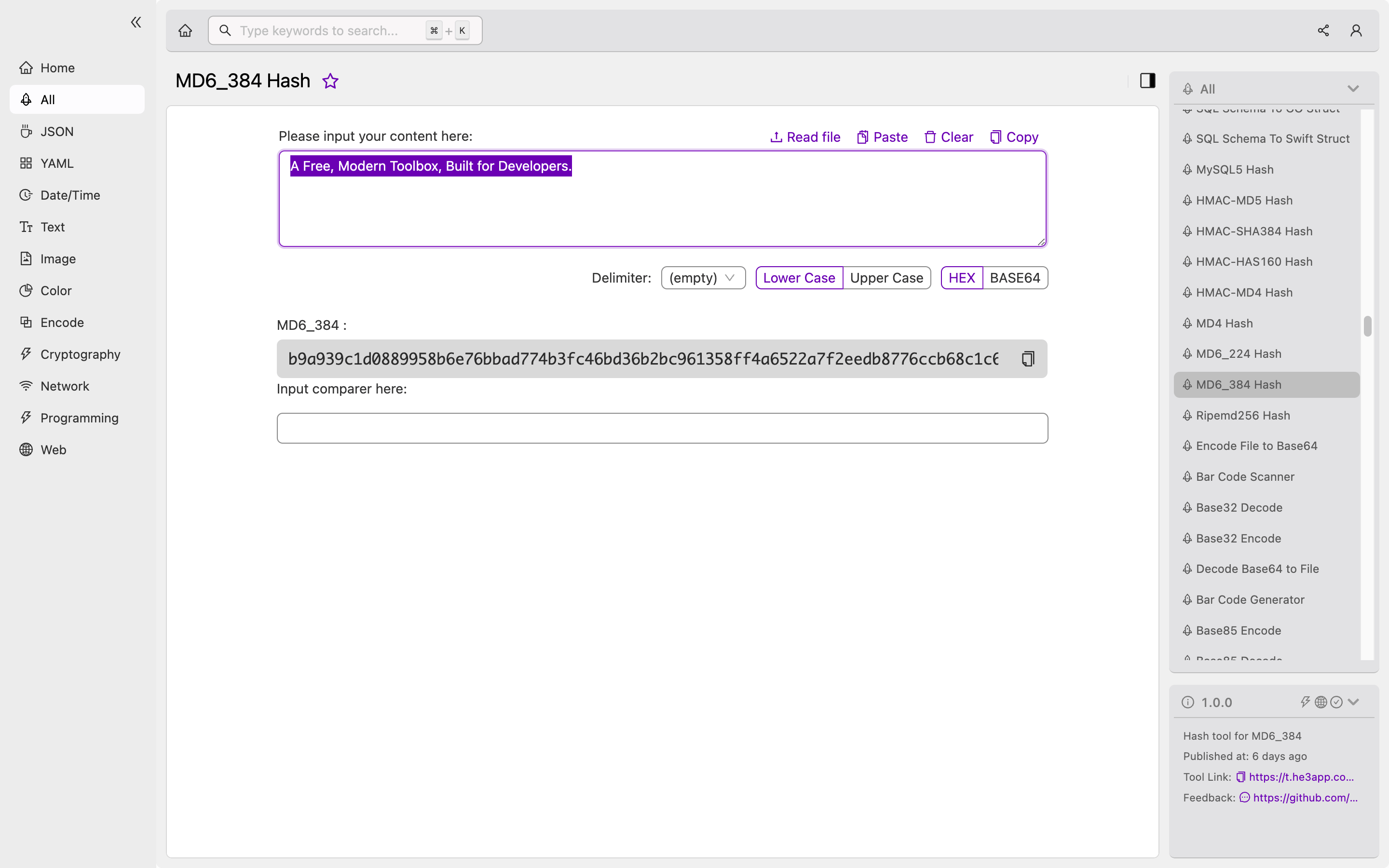
FAQ 3: How can I use MD6_384 Hash in my project?
You can use MD6_384 Hash tool in He3 Toolbox (https://t.he3app.com?fd6u) easily. Alternatively, you can implement the MD6_384 Hash algorithm in your project using programming languages such as Python, C++, or Java.
Conclusion
In conclusion, MD6_384 Hash is a powerful cryptographic hash function that provides high security and data integrity. It is an ideal choice for developers working in cybersecurity, data encryption, and digital signature fields. By understanding its features, misconceptions, and FAQs, you can make an informed decision about whether to use MD6_384 Hash in your projects.
Reference links:
