As a developer, you are likely familiar with cryptographic hash functions such as SHA-1, SHA-2, and SHA-3. However, there is another hash function, SHA0, that is not commonly used today due to its security vulnerabilities. In this article, we will explore SHA0 Hash, how it works, its key features, common misconceptions, and scenarios where it can be used.
What is SHA0 Hash?
SHA0 (Secure Hash Algorithm 0) is a cryptographic hash function that was introduced in 1993 by the United States National Security Agency (NSA). It is the first iteration of the Secure Hash Algorithm family and generates a 160-bit hash value for a given message or data. SHA0 was designed to provide data integrity and authenticity, as well as non-repudiation of messages.
How does SHA0 Hash Work?
SHA0 Hash works by taking a message or data input and processing it through a series of mathematical functions to produce a fixed-length output, which is the hash value. The input message is divided into blocks of 512 bits, and each block is processed through a series of 80 rounds of calculations. The output of each round is then used as input to the next round until a final hash value is produced.
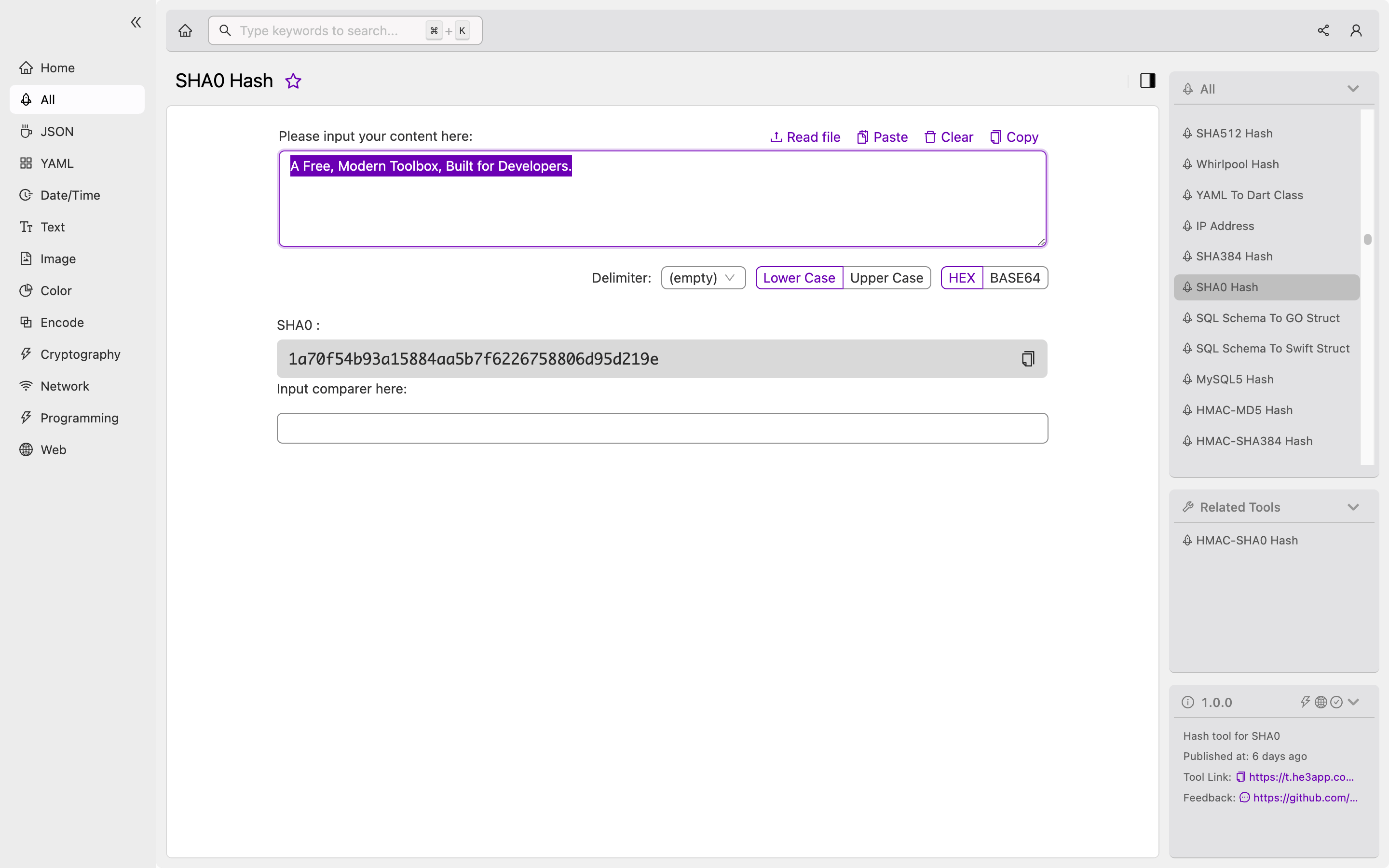
Here is an example of how to compute the SHA0 hash of a message using the command line:
echo -n "Hello, World!" | openssl dgst -sha0This will output the SHA0 hash value of the message “Hello, World!“. Or you can use SHA0 Hash tool in He3 Toolbox (https://t.he3app.com?9646) easily.
Scenarios for SHA0 Hash
While SHA0 is not recommended for new applications due to its vulnerabilities, it can still be used in some scenarios. One example is in legacy systems that still use SHA0 for compatibility reasons. Another scenario is in research or educational environments where the focus is on understanding the workings of cryptographic hash functions rather than on security.
Key Features of SHA0 Hash
Here are some key features of SHA0 Hash:
- Generates a 160-bit hash value
- Processes input data in 512-bit blocks
- Uses a series of 80 rounds of calculations
Misconceptions about SHA0 Hash
There are some misconceptions about SHA0 Hash, such as its security strength and its practical applications. Here are some common questions and answers regarding SHA0 Hash:
Is SHA0 Hash Secure?
No, SHA0 is no longer considered secure due to its vulnerability to collision attacks. Researchers have demonstrated that it is possible to create two different messages with the same SHA0 hash value, which could be exploited by attackers to cause data integrity and security issues.
Can SHA0 be Used for Password Hashing?
No, SHA0 is not recommended for password hashing as it is vulnerable to dictionary attacks and other forms of attack. Instead, developers should use stronger and more secure hash functions such as SHA-2 or SHA-3, as well as additional security measures such as salting and key stretching.
Conclusion
While SHA0 Hash is not commonly used today due to its security vulnerabilities, it is still worth understanding its concept and workings as a developer. Knowing the strengths and weaknesses of different hash functions can help you make informed decisions when choosing the right one for your application. For more information on SHA0 Hash and other cryptographic hash functions, check out the references below:
