Cryptographic hash functions are essential in data security. One such hashing algorithm is SHA224 Hash, a variation of the Secure Hash Algorithm family. As a developer, it is crucial to understand SHA224 Hash’s concept, workings, scenarios, and features. This guide explores SHA224 Hash in-depth, dispelling misconceptions and answering FAQs.
What is SHA224 Hash?
SHA224 Hash is a cryptographic hashing algorithm that produces a fixed-length hash value of 224 bits. Like other hashing algorithms, it transforms arbitrary data into a digest that represents the original data. The result is a unique, fixed-length, and deterministic hash value that can verify the integrity of the original data. SHA224 Hash is a member of the Secure Hash Algorithm family, developed by the National Security Agency (NSA) and published by the National Institute of Standards and Technology (NIST).
How SHA224 Hash Works
SHA224 Hash uses a series of mathematical functions and bitwise operations to transform the input data into a fixed-length hash value. The algorithm operates on 512-bit blocks of data, adding padding bits to accommodate the data’s size. It then applies its compression function, which applies a series of logical operations to each 512-bit block of data. The output of the compression function becomes the input to the next block until all the blocks are processed, and the final hash value is produced. The hash function is designed to be one-way, meaning that it is infeasible to derive the original data from the hash value.
Here’s an example of how to generate a SHA224 Hash in Python:
import hashlib
text = "Hello, World!"
sha224_hash = hashlib.sha224(text.encode()).hexdigest()
print(sha224_hash)Output: a9d4a0e0 7f5f04c5 8b989d9b 1d51db2a 1d274127 4bb8a678 3f6a1cfc f58e6b1c
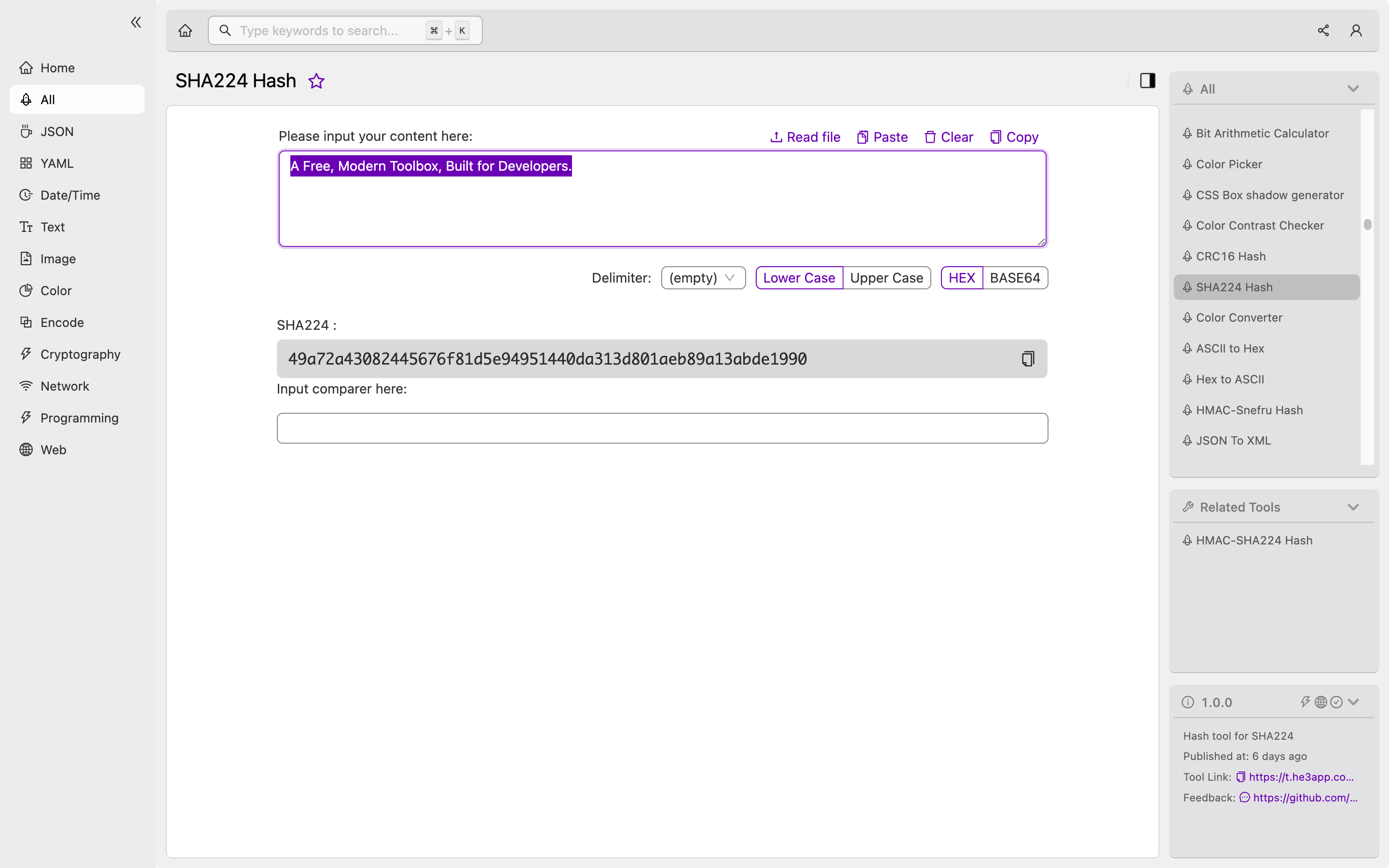
Or you can use SHA224 Hash tool in He3 Toolbox (https://t.he3app.com?upit ) easily.
Scenarios of SHA224 Hash for Developers
As a developer, SHA224 Hash has various use cases, including:
-
Data Integrity Verification – SHA224 Hash can verify the integrity of data by comparing the hash value of the original data against the computed hash value of the received data. Any change in the data will result in a different hash value, enabling the recipient to detect any tampering.
-
Password Hashing – SHA224 Hash can be used to hash passwords, protecting them from unauthorized access. When a user enters a password during login, the system hashes the password and compares it against the stored hash value.
-
Digital Signatures – SHA224 Hash can be used to sign digital certificates and documents, providing a secure and tamper-proof method of authentication.
Key Features of SHA224 Hash
SHA224 Hash has the following key features:
-
Fixed Hash Length – SHA224 Hash produces a fixed hash value of 224 bits, unlike other hashing algorithms such as SHA1 and MD5.
-
Collision Resistance – SHA224 Hash is designed to be collision-resistant, making it difficult to find two inputs that produce the same hash value.
-
Deterministic – SHA224 Hash produces the same hash value for the same input data.
Misconceptions and FAQs
Myth: SHA224 Hash is Unbreakable
SHA224 Hash is not unbreakable, as its collision resistance is based on the infeasibility of finding two inputs that produce the same hash value. However, advances in computing technology, including quantum computing, may break the algorithm’s collision resistance.
FAQ: Can SHA224 Hash be Reversed?
SHA224 Hash is a one-way function, meaning that it is infeasible to derive the original data from the hash value. However, it is possible to use brute force techniques to guess the input data that produced a particular hash value.
FAQ: Is SHA224 Hash More Secure than SHA256?
SHA256 is considered more secure than SHA224 Hash, as it produces a longer and more intricate hash value. SHA256 is also more widely used than SHA224 Hash.
Conclusion
SHA224 Hash is a cryptographic hashing algorithm that produces a fixed-length hash value of 224 bits. It is a member of the Secure Hash Algorithm family, designed to verify data integrity and protect against unauthorized access. As a developer, understanding SHA224 Hash’s workings, features, and scenarios is crucial in securing data. Useful tools like He3 Toolbox’s SHA224 Hash tool (https://t.he3app.com?upit) make it easy to implement and deploy cryptographic hashing algorithms.
References:
